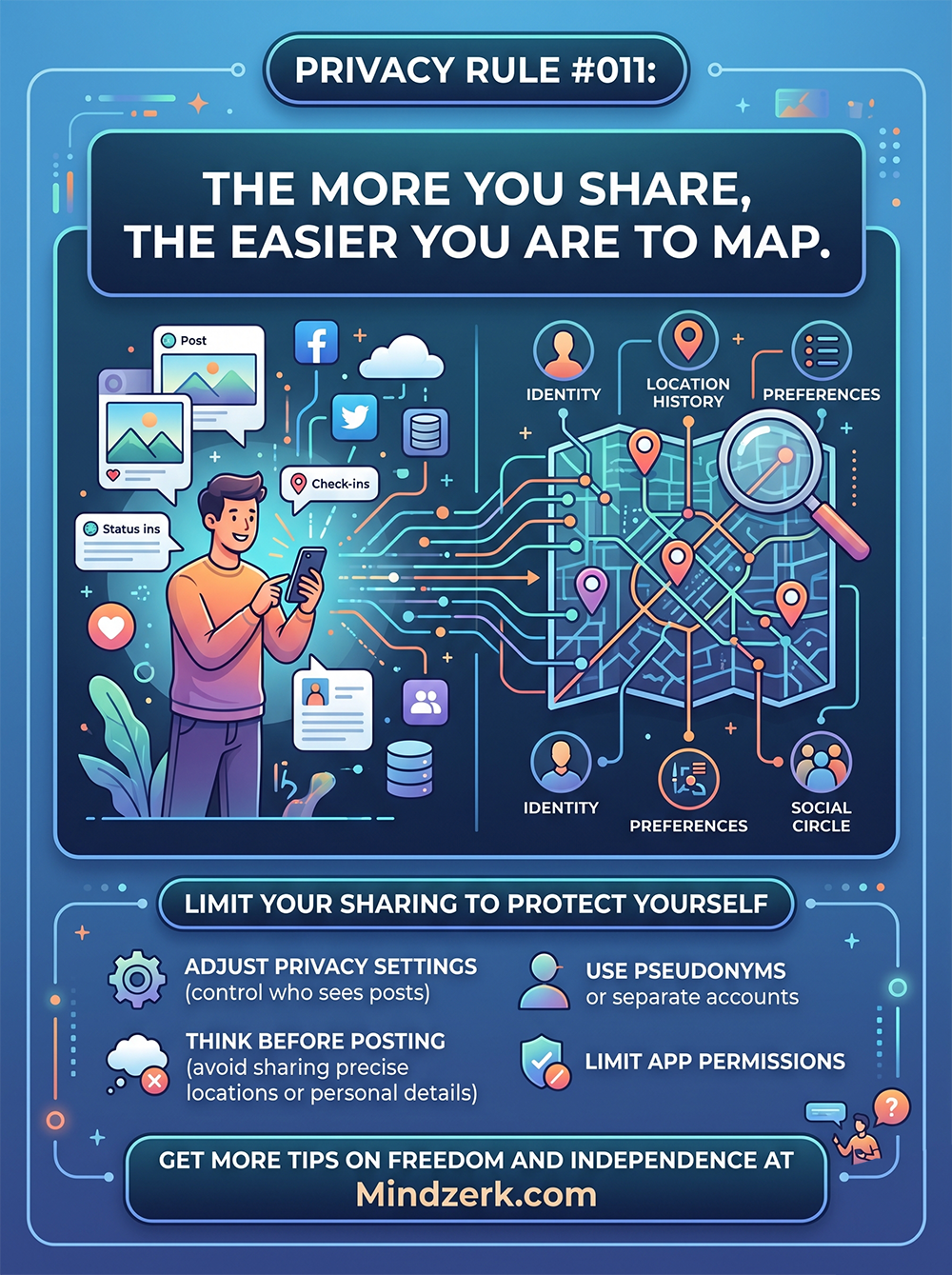
You don’t need to be hacked to be exposed.
You can map someone’s life just from what they willingly share.
- Posts
- Check-ins
- Photos
- Likes
- Comments
- App permissions
Piece by piece, it builds a profile.
And the more pieces you give away, the clearer the map becomes.
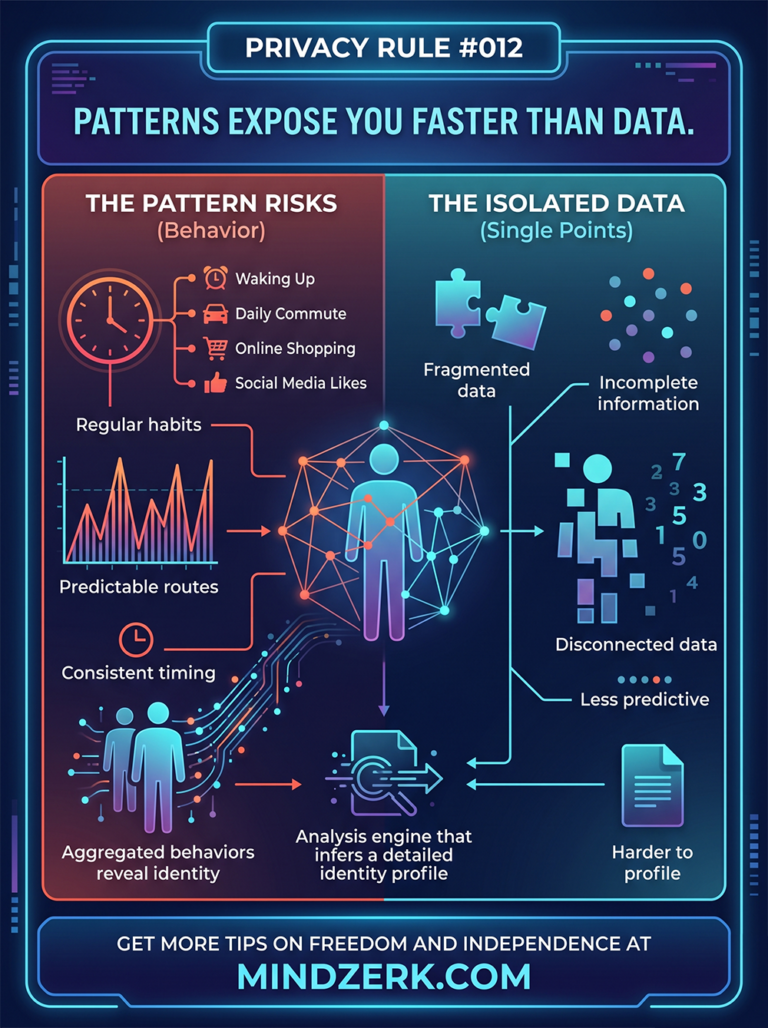
What “Being Mapped” Actually Means
It’s not just about your name or email.
It’s about patterns.
From your digital trail, someone (or something) can build:
- Your daily routines
- Your location habits
- Your relationships
- Your preferences
- Your vulnerabilities
Not from one post.
From all of them combined.
How It Happens (Without You Noticing)
You don’t post “everything.”
But you post enough.
Example:
- Morning coffee post → shows routine
- Gym check-in → shows location pattern
- Weekend photo → shows social circle
- Likes and follows → shows interests
- Comments → show opinions and mindset
Each one feels harmless.
Together, they create a detailed map.
The Real Risk
This isn’t just about ads.
Mapping enables:
- Targeted manipulation
- Identity profiling
- Social engineering attacks
- Physical tracking patterns
- Behavioral prediction
You become predictable. And predictable is exploitable.
The Illusion of “I Have Nothing to Hide”
That’s not the point.
Privacy isn’t about hiding.
It’s about control.
When you overshare:
- You lose control of context
- You lose control of timing
- You lose control of who sees what
And once it’s out, it’s permanent.
The Compound Effect of Sharing
One post = nothing.
100 posts = a story.
1,000 posts = a system someone else understands better than you do.
That’s where the problem starts.
How to Break the Map
You don’t need to disappear.
You need to be intentional.
1. Limit What You Share
Ask before posting:
- Does this reveal a pattern?
- Does this expose location or timing?
- Does this add unnecessary detail?
If yes, skip it.
2. Delay Your Posts
Don’t post in real time.
- Share after you leave
- Avoid live location signals
This alone removes a huge layer of risk.
3. Use Pseudonyms or Separate Accounts
Keep things segmented.
- Public identity
- Private identity
- Operational identity
Don’t blend them.
4. Lock Down App Permissions
Apps collect more than you think.
- Location
- Contacts
- Behavior
Turn off anything you don’t need.
5. Adjust Privacy Settings (But Don’t Rely on Them)
Settings help.
But they don’t solve the core issue:
You’re still the one providing the data.
The Mindset Shift
Stop thinking:
“Is this safe to post?”
Start thinking:
“What does this reveal when combined with everything else?”
That’s how mapping works.
A Simple Rule
If someone followed your posts for a month…
Could they predict:
- Where you go
- When you go
- Who you’re with
- What you care about
If yes, you’re overexposed.
The Balance
You don’t need to go silent.
You need to go selective.
Share:
- Ideas
- Value
- Perspectives
Limit:
- Location
- Timing
- Personal patterns
The Bottom Line
Every piece of information you share is a data point.
Enough data points become a map.
And maps make you easy to understand—and easier to exploit.
Final Thought
You don’t lose privacy all at once.
You lose it gradually, one post at a time.
Share less. Control more. Stay unpredictable.