Most people think hitting “delete” solves the problem.
It doesn’t.
It just hides it.
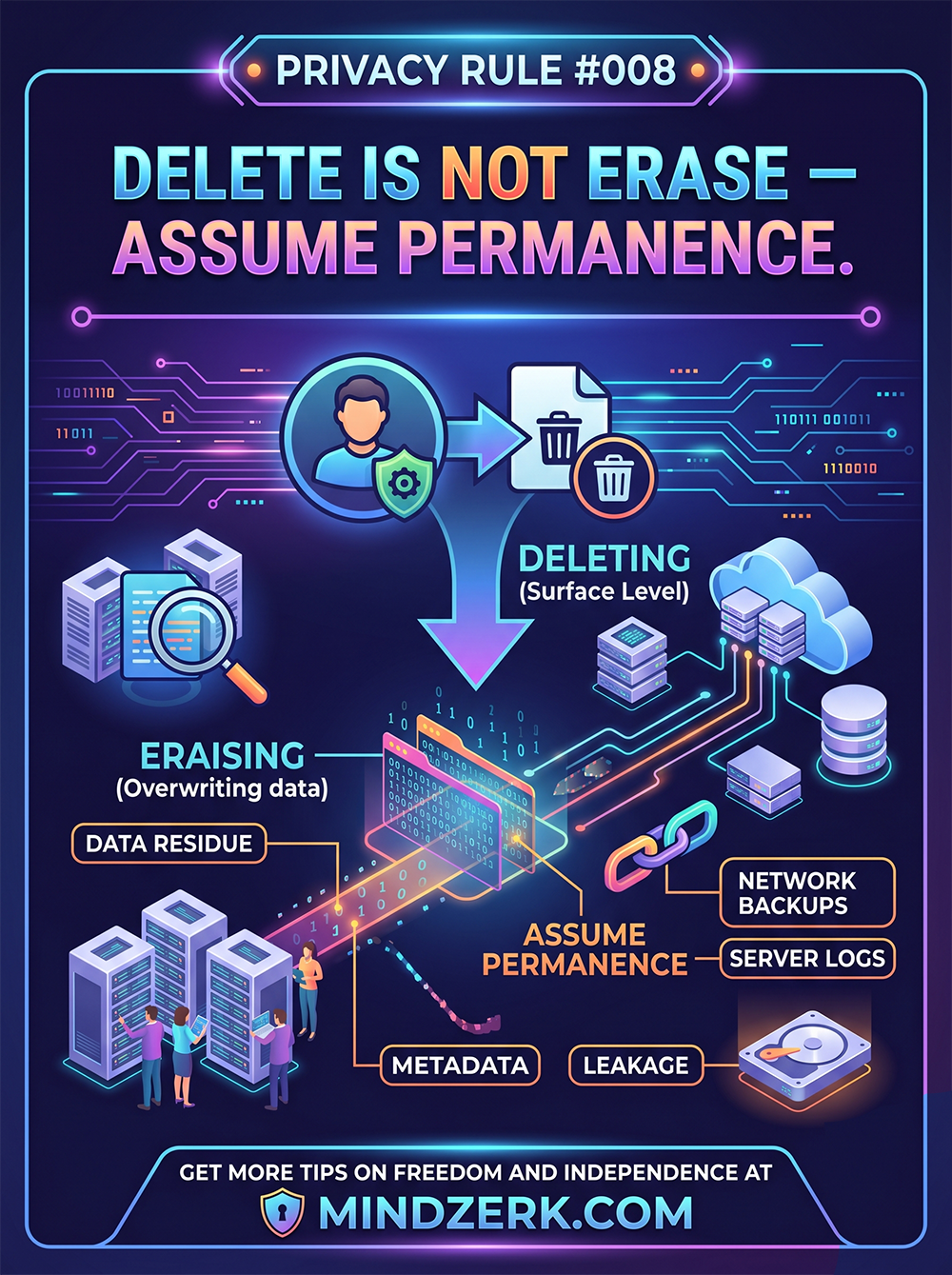
The Dangerous Illusion of Deleting
When you delete something online, you’re usually doing one thing:
Removing your view of it — not destroying the data itself.
Behind the scenes, that data can still exist in:
- Backups
- Server logs
- Cached systems
- Third-party databases
Deletion is often surface-level, not final.
What “Delete” Actually Means
In many systems, deleting a file or message:
- Removes the reference
- Marks space as reusable
- Leaves the data intact until overwritten
That’s it.
The data can still be recovered, reconstructed, or accessed in other forms.
Real-World Data Footprints
Even if you delete something:
- Platforms may retain copies
- Emails may live on in inboxes
- Screenshots may already exist
- Logs may track the interaction
And once data spreads…
You don’t control it anymore.
The Layers You Don’t See
1. Backups
Companies keep backups for reliability.
Your “deleted” data can live there for:
- Days
- Months
- Sometimes years
2. Metadata
Even if content is gone, metadata remains:
- Timestamps
- IP addresses
- Device info
- Interaction patterns
That alone can tell a story.
3. Network Copies
Data travels.
It can pass through:
- Servers
- CDNs
- APIs
- Third-party tools
Each hop is another potential copy.
4. Human Behavior
This is the biggest wildcard.
People:
- Save things
- Share things
- Screenshot everything
Once someone else has it, deletion is irrelevant.
The Rule: Assume Permanence
If you wouldn’t want it permanent, don’t send it.
That’s the simplest version.
Not paranoid. Just realistic.
How to Operate With This Rule
Think Before You Create
Pause before posting, sending, or uploading.
Ask:
- Would I be okay with this resurfacing later?
Minimize What You Share
Less data = less risk.
- Avoid oversharing
- Strip unnecessary details
- Keep things tight
Use Better Tools (When It Matters)
Some tools prioritize privacy more than others.
But even then:
- Don’t assume total control
- Don’t assume full deletion
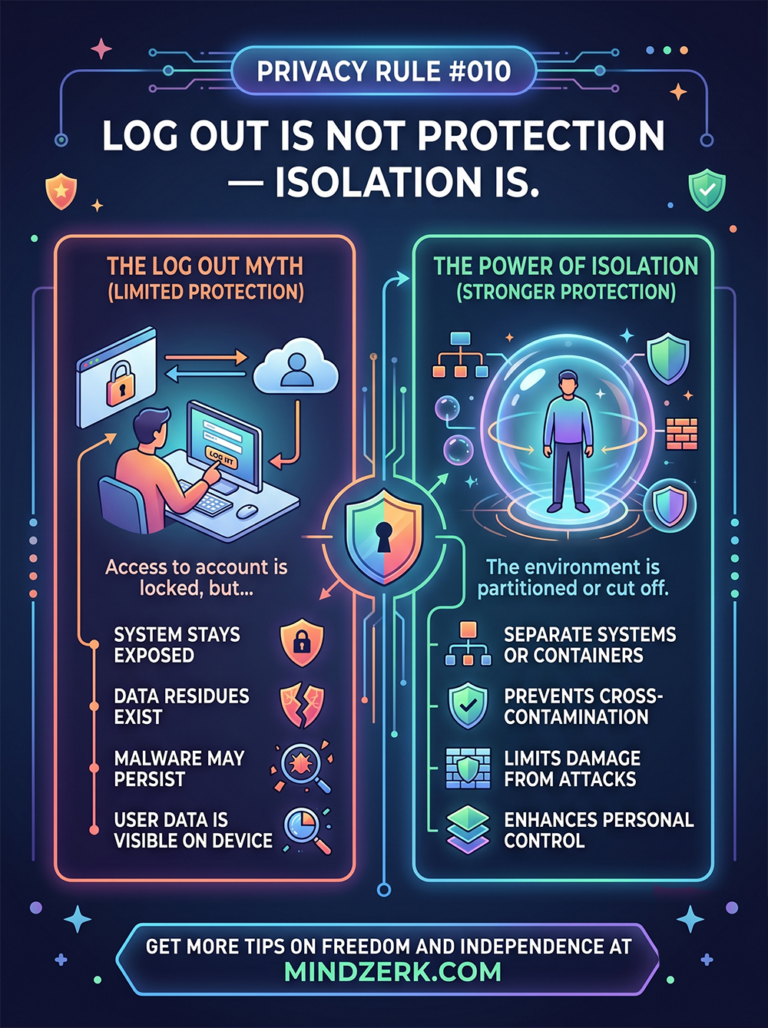
Separate Sensitive Activity
Keep high-risk or personal actions isolated.
Different accounts. Different environments.
Limit overlap.
Control the Lifespan (When Possible)
Some platforms offer:
- Expiring messages
- Temporary links
Use them—but don’t rely on them.
They reduce risk. They don’t eliminate it.
The Mindset Shift
Most people operate like this:
“I can delete it later.”
That’s backwards.
You should operate like this:
“This could exist forever.”
Why This Matters More Than Ever
Data is currency.
Your behavior, interests, and patterns are:
- Collected
- Analyzed
- Sold
- Stored
Even small pieces add up.
The Bottom Line
Deletion is not destruction.
It’s a convenience feature.
Privacy isn’t about cleaning up after the fact. It’s about controlling what exists in the first place.
Final Thought
Act like everything leaves a trace.
Because it does.
In a digital world, permanence is the default—not the exception.